Kako bi razdvojio gostinsku mrežu od lokalne, napravljena su dva VLAN.
WiFi je ubiquity UniFi, na samim access pontima su ssid-ovi upareni sa vlan-ovima.
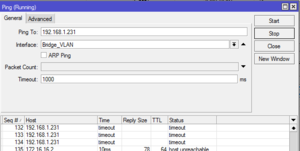
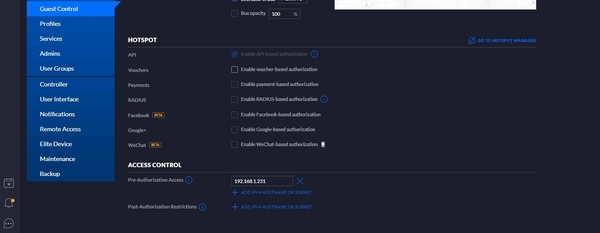
Sve funkcionise, a dodatno mi je potrebno da NAS (192.168.1.231) koji je u LAN bude dostupan i kroz gostinski WiFi / VLAN.
Pristupanje NAS je dovoljno samo preko SMB i http.
(Ne mora nista da se propušta na temu DLNA i slicnih pizdarija što se oslanjaju na multicasting/broadcasting).
Sledi config rutera, malo redigovan zbog privatnosti (javne IP, useri i lozinke).
Ako imate dodatna pitanja, ponešto ću znati da odgovorim.
Verovatno neću umeti da odgovorim koja ideja stoji iza nečega, pokušao sam da kontaktiram čoveka koji mi je ovo konfigurisao - bezuspešno.
Hvala unapred.
# Mar/10/2020 20:03:22 by RouterOS 6.45.7
# software id = 7DCL-WT6S
#
# model = RouterBOARD 3011UiAS
# serial number = xxxxxxxxxxxx
/interface bridge
add name=Bridge_Corp
add name=Bridge_VLAN
/interface ethernet
set [ find default-name=ether1 ] name=ether1-ISP
set [ find default-name=ether2 ] name=ether2-DVR
set [ find default-name=ether3 ] name=ether3-Alarm
set [ find default-name=ether5 ] name=ether5-Unifi
set [ find default-name=ether6 ] name=ether6
set [ find default-name=ether7 ] name=ether7
/interface pptp-client
add connect-to=xxxxxxxxxxxxxxxxxx disabled=no name=remotevpn \
password="xxxxxxxxxxxxx" user=xxxxxx
/interface vlan
add interface=ether5-Unifi name=vlan100eth5 vlan-id=100
add interface=ether6 name=vlan100eth6 vlan-id=100
add interface=ether7 name=vlan100eth7 vlan-id=100
/interface list
add name=WAN
add name=LAN-Corp
add name=LAN-Guest
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/ip pool
add name=Pool_Corp ranges=192.168.1.30-192.168.1.254
add name=Pool_VLAN ranges=172.16.16.3-172.16.16.254
add name=Pool_VPN ranges=192.168.89.2-192.168.89.255
/ip dhcp-server
add address-pool=Pool_Corp disabled=no interface=Bridge_Corp name=DHCP_Corp
add address-pool=Pool_VLAN disabled=no interface=Bridge_VLAN name=DHCP-VLAN
/ppp profile
set *FFFFFFFE local-address=Pool_VPN remote-address=Pool_VPN use-upnp=yes
/interface bridge port
add bridge=Bridge_Corp interface=ether2-DVR
add bridge=Bridge_Corp interface=ether5-Unifi
add bridge=Bridge_VLAN interface=vlan100eth5
add bridge=Bridge_Corp interface=ether6
add bridge=Bridge_VLAN interface=vlan100eth6
add bridge=Bridge_Corp interface=ether7
add bridge=Bridge_VLAN interface=vlan100eth7
add bridge=Bridge_Corp interface=ether3-Alarm
add bridge=Bridge_Corp interface=ether8
/interface l2tp-server server
set enabled=yes ipsec-secret=xxxxxxxxxxxx use-ipsec=yes
/interface list member
add interface=ether1-ISP list=WAN
add interface=Bridge_Corp list=LAN-Corp
add interface=Bridge_VLAN list=LAN-Guest
/interface pptp-server server
set enabled=yes
/ip address
add address=192.168.1.2/24 interface=Bridge_Corp network=192.168.1.0
add address=172.16.16.2/24 interface=Bridge_VLAN network=172.16.16.0
add address=xxx.xxx.xxx.xxx/29 interface=ether1-ISP network=xxx.xxx.xxx.xxx
/ip cloud
set ddns-enabled=yes
/ip dhcp-client
add dhcp-options=hostname,clientid disabled=no interface=ether1-ISP
/ip dhcp-server lease
add address=192.168.1.231 client-id=1:e0:46:9a:a0:88:a4 mac-address=\
xx:xx:xx:xx:xx:xx server=DHCP_Corp
add address=172.16.16.18 client-id=1:94:9f:3e:57:71:28 mac-address=\
xx:xx:xx:xx:xx:xx server=DHCP-VLAN
/ip dhcp-server network
add address=172.16.16.0/24 dns-server=8.8.8.8,xxx.xxx.xxx.xxx,xxx.xxx.xxx.xxx \
gateway=172.16.16.2
add address=192.168.1.0/24 dns-server=8.8.8.8,xxx.xxx.xxx.xxx,xxx.xxx.xxx.xxx \
gateway=192.168.1.2
/ip dns
set allow-remote-requests=yes cache-max-ttl=6h servers=\
8.8.8.8,xxx.xxx.xxx.xxx,xxx.xxx.xxx.xxx
/ip firewall filter
add action=accept chain=input dst-port=8280,18291 in-interface-list=WAN \
protocol=tcp
add action=accept chain=input dst-port=500,1701,4500 in-interface-list=WAN \
protocol=udp
add action=accept chain=input protocol=ipsec-esp
add action=accept chain=input protocol=ipsec-ah
add action=accept chain=input comment="allow pptp" dst-port=1723 protocol=tcp
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment=" --- test to access to NAS ---" \
dst-address=192.168.1.231 log=yes log-prefix=dlna- src-address=\
172.16.16.18
add action=accept chain=input comment=" --- test to access to NAS ---" \
dst-address=172.16.16.18 log=yes log-prefix=dlna- src-address=\
192.168.1.231
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=drop chain=forward in-interface=Bridge_VLAN out-interface=\
Bridge_Corp
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat \
connection-state=new in-interface-list=WAN
/ip firewall nat
add action=masquerade chain=srcnat comment="------- NAT -------" \
out-interface-list=WAN
add action=dst-nat chain=dstnat comment="--- Remote Access DVR Port80 ---" \
dst-port=80 in-interface=ether1-ISP protocol=tcp to-addresses=\
192.168.1.10
add action=dst-nat chain=dstnat comment="--- Remote Access NAS ---" dst-port=\
8088 in-interface=ether1-ISP protocol=tcp to-addresses=192.168.1.231 \
to-ports=443
add action=dst-nat chain=dstnat comment="--- Remote Access Printer ---" \
disabled=yes dst-port=8080 in-interface=ether1-ISP protocol=tcp \
to-addresses=192.168.1.142 to-ports=80
add action=dst-nat chain=dstnat comment="--- Remote Access DVR Port554 ---" \
dst-port=554 in-interface=ether1-ISP protocol=tcp to-addresses=\
192.168.1.10
add action=dst-nat chain=dstnat comment="--- Remote Access DVR Port8000 ---" \
dst-port=8000 in-interface=ether1-ISP protocol=tcp to-addresses=\
192.168.1.10
add action=dst-nat chain=dstnat comment="--- Harping NAT ---" dst-address=\
xxx.xxx.xxx.xxx dst-address-type=local dst-port=8000 protocol=tcp \
to-addresses=192.168.1.10 to-ports=8000
add action=dst-nat chain=dstnat comment="--- Harping NAT ---" dst-address=\
xxx.xxx.xxx.xxx dst-address-type=local dst-port=554 protocol=tcp \
to-addresses=192.168.1.10 to-ports=554
add action=dst-nat chain=dstnat comment="--- Harping NAT ---" dst-address=\
xxx.xxx.xxx.xxx dst-address-type=local dst-port=80 protocol=tcp \
to-addresses=192.168.1.10 to-ports=80
add action=masquerade chain=srcnat comment="--- Harping NAT ---" dst-address=\
192.168.1.10 dst-port=8000 out-interface=Bridge_Corp protocol=tcp \
src-address=192.168.1.0/24
add action=masquerade chain=srcnat comment="--- Harping NAT ---" dst-address=\
192.168.1.10 dst-port=80 out-interface=Bridge_Corp protocol=tcp \
src-address=192.168.1.0/24
add action=masquerade chain=srcnat comment="--- Harping NAT ---" dst-address=\
192.168.1.10 dst-port=554 out-interface=Bridge_Corp protocol=tcp \
src-address=192.168.1.0/24
add action=masquerade chain=srcnat comment="--- Harping NAT ---" \
out-interface=remotevpn
/ip route
add distance=1 gateway=xxx.xxx.xxx.xxx
add distance=1 dst-address=192.168.10.0/24 gateway=remotevpn
/ip service
set telnet disabled=yes
set ftp disabled=yes
set www port=8280
set ssh disabled=yes
set api disabled=yes
set api-ssl disabled=yes
/ip upnp
set enabled=yes
/ip upnp interfaces
add interface=Bridge_Corp type=internal
add interface=Bridge_VLAN type=internal
/ppp secret
add name=xxxxxx password=xxxxxxxxxxxxxxxxxxxx
add name=xxxxxx password=xxxxxxxxxxxxxxxxxxxx
/system identity
set name="xxxxxxxxxxxxxxxxxxx"
/tool graphing interface
add interface=ether1-ISP
add interface=Bridge_Corp
add interface=Bridge_VLAN
/tool graphing resource
add




 Rutiranje izmedju dva VLAN
Rutiranje izmedju dva VLAN